Ledger Hardware Wallet Security: Complete Advanced Protection Guide
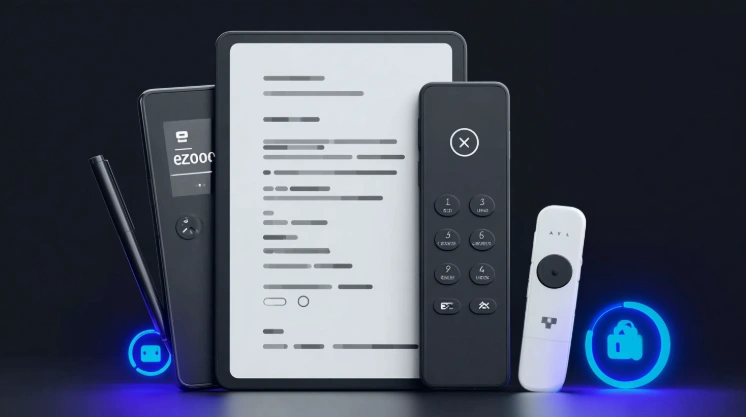
Ledger Hardware Wallet Security encompasses multiple protection layers defending cryptocurrency holdings against digital and physical threats through sophisticated defense mechanisms. The Ledger anti-phishing capabilities combined with secure transaction approval processes create comprehensive protection that exceeds basic cold storage security. Understanding these advanced features enables users to maximize protection while maintaining convenient access to private keys.
The security architecture integrates hardware-level protection through the certified secure element with software verification through Ledger Live applications. Each transaction requires explicit device confirmation, preventing remote attacks regardless of computer or network compromise. This multi-layered approach addresses threat vectors that single-point security solutions cannot adequately protect against.
This guide covers anti-phishing mechanisms, transaction security, firmware integrity, credential protection, and physical safety for complete crypto security across all supported coins via USB-C or Bluetooth connection.
Anti-Phishing Protection

Anti-Phishing Protection within Ledger hardware wallet security addresses the most common attack vector targeting cryptocurrency users through deceptive websites and communications. The device verification prompt requires hardware confirmation preventing software-only attacks while safe URL confirmation guides users toward legitimate resources. Understanding phishing defense maximizes protection against social engineering.
Phishing attacks attempt to steal credentials or trick users into signing malicious transactions. Hardware wallet architecture provides inherent protection by requiring physical device interaction for any sensitive operation for cold wallet security.
Device Verification Prompt
Device verification prompt security features:
| Feature | Protection | User Action |
|---|---|---|
| Transaction display | Shows actual details | Compare to intended |
| Address verification | Full address shown | Confirm recipient |
| Amount confirmation | Exact value displayed | Verify correctness |
| Network identification | Blockchain specified | Check asset type |
| Button confirmation | Physical approval | Press to sign |
Device verification prompt ensures all critical information displays on trusted hardware screen rather than potentially compromised computer display. This Ledger anti-phishing mechanism prevents blind signing attacks for secure transaction approval.
Safe URL Confirmation
- Always access Ledger Live from ledger.com only
- Verify HTTPS connection before any interaction
- Check for exact domain spelling without variations
- Avoid links from emails or social media
- Bookmark official sites for future access
- Recognize that Ledger never sends login links
- Report suspected phishing sites to Ledger security
Safe URL confirmation prevents credential theft through fake website impersonation. Official Ledger resources use consistent domains without variations for private keys protection unlike Trezor or KeepKey URL verification approaches.
Transaction Signing Security

Transaction Signing Security represents core Ledger hardware wallet security functionality protecting every cryptocurrency operation. The multi-step confirmation process ensures intentional approval while offline verification occurs within the secure element isolated from network threats. Transaction security prevents unauthorized transfers regardless of software compromise.
Every transaction requires explicit hardware wallet approval through physical button presses. No software can bypass this requirement, ensuring users maintain complete control over cold storage operations.
Multi-Step Confirmation
Multi-step confirmation transaction workflow:
- Create transaction in Ledger Live or connected app
- Transaction details sent to hardware wallet
- Device displays recipient address
- Verify address matches intended destination
- Device displays transaction amount
- Confirm amount is correct
- Device displays network fee
- Approve fee amount
- Press both buttons to sign
- Signed transaction broadcasts to network
Multi-step confirmation ensures deliberate approval of each transaction element during secure transaction approval. Rushing through confirmation steps defeats the purpose of Ledger anti-phishing protection for crypto security.
Offline Verification
| Component | Function | Security Benefit |
|---|---|---|
| Secure element | Key storage | Hardware isolation |
| Internal display | Transaction review | Trusted output |
| Button input | User confirmation | Physical approval |
| Cryptographic signing | Transaction authorization | Private key isolation |
| No network access | Key operations | Air-gapped security |
Offline verification ensures private keys never exist outside the secure element during transaction signing. The Ledger hardware wallet security architecture maintains key isolation throughout all operations via USB-C or Bluetooth across all supported coins.
Firmware Integrity
Firmware Integrity verification ensures device software remains authentic and unmodified throughout ownership. The Ledger Live check confirms firmware authenticity while signature verification validates update origin. Maintaining firmware integrity prevents compromised software from affecting cold wallet operations.
Regular firmware verification provides ongoing security assurance. Compromised firmware could potentially expose private keys or manipulate transaction displays, making integrity crucial for private keys protection.
Ledger Live Check
- Connect device to Ledger Live application
- Application performs genuine check automatically
- Cryptographic attestation verifies secure element
- Green checkmark confirms authentic device
- Failed check indicates potential compromise
- Regular verification recommended monthly
- Always check after firmware updates
Ledger Live check provides cryptographic proof of device authenticity through Ledger hardware wallet security verification. The attestation process confirms both hardware and firmware integrity for secure element validation.
Signature Verification
| Layer | Verification | Protection |
|---|---|---|
| Update file | Ledger signature | Authentic source |
| Installation | Secure element validation | Integrity check |
| Boot process | Internal verification | Execution safety |
| Runtime | Continuous monitoring | Operation security |
| Rollback prevention | Version control | Downgrade protection |
Signature verification ensures only authentic Ledger firmware executes on devices. The secure element refuses unsigned code regardless of installation attempts for Ledger anti-phishing and malware protection unlike Trezor or KeepKey firmware verification.
Passphrase and PIN Security

Passphrase and PIN Security creates access control layers protecting Ledger hardware wallet security against unauthorized device use. The strong PIN setup establishes primary access barrier while optional passphrase adds advanced protection creating hidden wallets. Credential security complements hardware protection for complete private keys security.
PIN and passphrase operate independently, each providing distinct security benefits. PIN controls device access while passphrase creates separate wallet derivation for cold storage protection.
Strong PIN Setup
- Select 4-8 digit PIN length
- Avoid sequential numbers (1234, 5678)
- Avoid repeated digits (0000, 1111)
- Do not use birthdays or anniversaries
- Create unique code not used elsewhere
- Memorize without written storage
- Three incorrect attempts wipes device
- PIN entry only occurs on device display
Strong PIN setup creates effective access barrier for secure transaction approval. Device wipe after three failures protects against brute force attempts for crypto security across all supported coins.
Optional Passphrase
| Feature | Function | Consideration |
|---|---|---|
| Hidden wallet | Separate derivation | Additional security |
| Plausible deniability | Decoy standard wallet | Theft protection |
| No storage | User memorization | Loss risk |
| Any string valid | Unlimited options | Complexity choice |
| Case sensitive | Exact matching | Precision required |
Optional passphrase creates advanced Ledger hardware wallet security through hidden wallet functionality. Passphrase usage requires careful management to avoid permanent access loss for private keys via USB-C or Bluetooth.
Physical Device Safety
Physical Device Safety addresses physical security aspects of Ledger hardware wallet security complementing digital protections. The tamper-proof packaging confirms genuine device receipt while secure storage location protects ongoing physical possession. Physical safety prevents attacks requiring device access.
Physical security should match digital protection levels. Sophisticated digital security becomes irrelevant if physical device access enables tampering or theft for cold wallet protection.
Tamper-Proof Packaging
- Holographic seal on box opening
- Security tape with void indication
- Factory-sealed plastic wrap
- Sealed recovery card envelope
- USB cable in original packaging
- Anti-counterfeit features on labels
Tamper-proof packaging confirms genuine, unmodified device receipt during Ledger anti-phishing and supply chain verification. Any seal irregularities warrant investigation before device use for secure element protection.
Secure Storage Location
| Location | Security Level | Accessibility |
|---|---|---|
| Personal safe | High | Convenient |
| Hidden location | Medium-High | Private |
| Bank safe deposit | Very High | Limited hours |
| Secure drawer | Medium | Very convenient |
| Travel storage | Variable | Portable |
Secure storage location protects physical device from theft or unauthorized access. The Ledger hardware wallet security depends on both digital and physical protection for private keys safety unlike Trezor or KeepKey physical security.
For threat models, see our Ledger Wallet Threat Models & Protection guide. For anti-phishing details, visit Ledger Anti-Phishing & Transaction Verification.
Frequently Asked Questions
-
Private keys never leave the secure element chip. All signing occurs on isolated hardware. Software wallets expose keys to computer memory where malware can capture them.
-
Transaction details display on trusted hardware screen rather than computer display. Users verify recipient address and amount on device before physical button approval.
-
No, provided you verify transaction details on device screen. Malware cannot modify what displays on hardware wallet or forge physical button presses.
-
Compromised firmware could manipulate transaction displays or leak private keys. Verification ensures only authentic Ledger code runs on your device.
-
Passphrase provides additional security for high-value holdings but adds complexity. Consider if you can reliably manage the additional credential without loss.
-
Verify through Ledger Live monthly during regular use. Always verify after firmware updates or if device was outside your possession.
-
They cannot access funds without PIN. Three incorrect PIN attempts wipe the device. Without recovery phrase, thief cannot recover wallet.